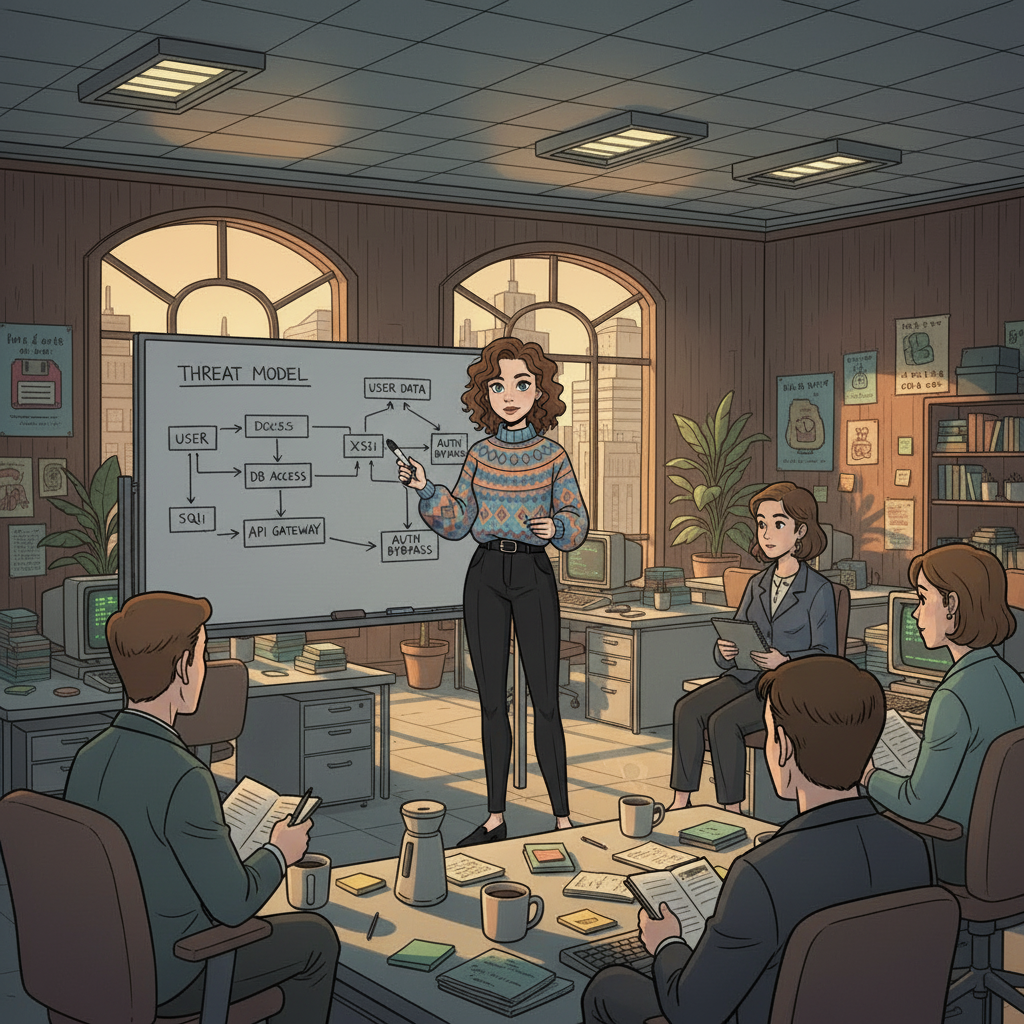
Threat Modeling
Understanding potential attack vectors helps prepare defenses — crucial for IT operations and compliance teams.

Loss of key incident logs hampers response efforts.

Team struggles with undocumented system configurations.

Compliance confusion escalates without clear documentation.

Increased alert fatigue from a missing threat model context.
Knowledge loss leads to significant operational gaps that hinder security posture.
Prioritize documenting threat models and incident response procedures.
Undocumented workflows and shadow systems can jeopardize security continuity.
Schedule a comprehensive knowledge transfer interview and initiate critical documentation.
When a security engineer departs, the organization faces multiple risks that manifest in real operational challenges, particularly around incident response and vulnerability management.
With the security engineer's knowledge gone, teams might overlook critical vulnerabilities that require immediate attention. This leads to:
Incident response times can dramatically increase because:
Critical vendor contacts may leave with the employee, causing:
This lack of information leads to cumbersome processes where each decision requires more time and effort, creating a cumbersome burden and hindering organizational agility.

The departure of a security engineer does not merely create knowledge gaps; it allows for unraveling layers of crucial operational knowledge that ensures security integrity.
Understanding these knowledge domains is crucial for a smooth transition and maintaining security posture during periods of change.
An AI-guided interview can uncover intricate aspects of a security engineer's responsibilities that are typically undocumented.
These pointed inquiries empower the organization to clearly view what critical knowledge may be lost and how to effectively manage this transition.

A thorough knowledge transfer report ensures that a departing security engineer’s responsibilities are transparently communicated and outlined.
Operational Playbooks
Documenting step-by-step procedures for handling common security incidents.
Decision Rationale Documentation
Contextual insights into why specific security configurations were put in place.
System Documentation
Clarity on how systems interconnect and the roles they play in security.
Risk Assessments
Evaluating potential vulnerabilities and suggesting mitigations based on previously established frameworks.
Handover Checklists
Protocols that ensure nothing critical is overlooked during an employee transition.
Having these resources prepared acts as a safety net against critical knowledge gaps and ensures security resilience.

This checklist outlines the key actions to take for a smooth transfer of knowledge from departing security engineers.
Ensure thorough records of current threat scenarios and mitigations are updated before departure.
Revise playbooks to reflect current practices and document based on past incidents.
Outline who has access to which systems and the rationale behind custom configurations.
Ensure that all vulnerabilities tracked in tools like Nessus have clear remediation paths documented.
Facilitate meetings to review all critical security knowledge and answer any lingering questions from the team.
Understanding potential attack vectors helps prepare defenses — crucial for IT operations and compliance teams.
Defined steps ensure quick actions during security incidents, empowering efficient recovery.
Maintaining clear access protocols is essential for security — relevant for IAM systems.
The manager learns the Security Engineer is leaving and initiates the knowledge transfer process.
An AI-guided interview session is scheduled with the departing Security Engineer to systematically capture institutional knowledge.
The AI interview extracts undocumented workflows, vendor relationships, decision rationale, and operational edge cases.
A structured knowledge transfer report is produced, covering all critical domains, handover checklists, and risk areas.
The team reviews the report, identifies remaining gaps, and completes the handover before the departure date.
The organization faces knowledge gaps, slower incident responses, and potential compliance failures, impacting overall security.
Schedule systematic interviews to capture undocumented workflows and review existing threats and vulnerabilities.
Ideally, knowledge transfer should begin immediately upon notice and may take 1-2 weeks depending on complexity.